Table of Contents
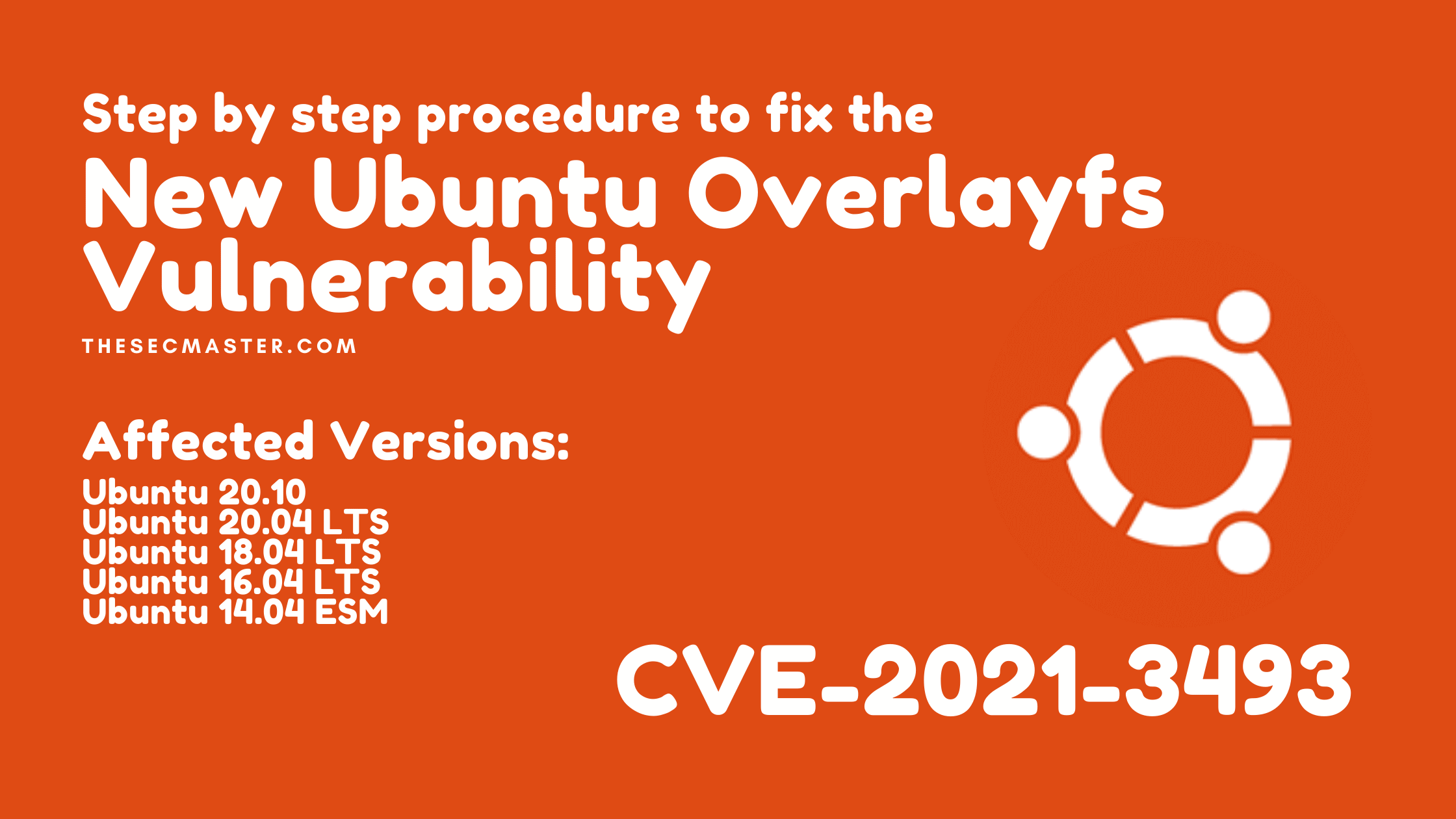
Step by Step Procedure to Fix the New Ubuntu Overlayfs Vulnerability (CVE-2021-3493)
Linux |
You might have read that a new critical Ubuntu overlayfs vulnerability was discovered and registered under CVE-2021-3493 in mid-April 2021. This article covers not only information about the Ubuntu overlayfs vulnerability. It covers how to find the vulnerable host and how to fix the new Ubuntu overlayfs vulnerability (CVE-2021-3493) found on a vulnerable host.
Timeline of This Vulnerability:
An independent researcher reported this vulnerability in the early days of April 2021.
On 12th April 2021, the vulnerability was registered in National Vulnerability Database (NVD) under CVE-2021-3493.
Ubuntu published this vulnerability with security advisories on 15th April 2021.
About the New Ubuntu Overlayfs Vulnerability (CVE-2021-3493):
This is a new critical vulnerability that actually is not on the operating system, but it exists on the kernel of the operating system. The vulnerability is due to the overlayfs implementation in the Linux kernel, which did not properly validate the application of file system capabilities with respect to use namespaces. A local user can use this Ubuntu overlayfs vulnerability to gain root privileges without authentication.
Ubuntu Versions Vulnerable to New Ubuntu Overlayfs Vulnerability (CVE-2021-3493):
This is a Ubuntu-specific vulnerability. This could be seen on some Debian distros too. Other popular Linux distributions: RedHat and Suse confirmed that the vulnerability doesn’t exist on their distros. Few reference links are shared here below.
Ubuntu 20.10
Ubuntu 20.04 LTS
Ubuntu 18.04 LTS
Ubuntu 16.04 LTS
Ubuntu 14.04 ESM
Technical Details of the New Ubuntu Overlayfs Vulnerability (CVE-2021-3493)
Linux supports file capabilities stored in extended file attributes that work similarly to setuid-bit but can be more fine-grained. A simplified procedure for setting file capabilities in pseudo-code looks like this:
setxattr(…):
if cap_convert_nscap(…) is not OK:
then fail
vfs_setxattr(…)
The important call is cap_convert_nscap, which checks permissions with respect to namespaces.
If we set the file capabilities from our own namespace and on our own mount, there is no problem, and we have permission to do so. The problem is that when OverlayFS forwards this operation to the underlying file system, it only calls vfs_setxattr and skips checks in cap_convert_nscap.
This allows setting arbitrary capabilities on files in the outer namespace/mount, where they will also be applied during execution.
In Linux 5.11, the call to cap_convert_nscap was moved into vfs_setxattr, so it is no more vulnerable.
How to Test the New Ubuntu Overlayfs Vulnerability (CVE-2021-3493) On The Host?
Check the version of the kernel running on your Ubuntu server. Open the terminal and issue this command to check the version of Ubuntu:
$ cat /etc/os-release
in our case, we are running 20.04 LTS which is vulnerable to Ubuntu overlayfs vulnerability (CVE-2021-3493)
2. The exploit is available to the public in GitHub. Download the exploit and execute. We have downloaded the exploit on the desktop for demonstration purposes.
Optional: You can verify the user with ‘whoami‘ command. In this case we are log in to a normal user account.
Change the directory to Desktop.
$ cd Desktop/CVE-2021-3493-main/
Set executable permission for ‘exploit.c‘ using ‘chmod’ command:Enter the root password to execute the command.
$ sudo chmod +x exploit.c
First compel the ‘exploit.c’ file and store the compelled file to ‘execure.out‘ using a gcc compiler.
$ gcc exploit.c -o exploit
As soon as you execute the compelled file. You will see root command prompt without authentication.
This is how you can test the new Ubuntu overlayfs vulnerability (CVE-2021-3493) on the host.
How to Install Gcc Compiler On Ubuntu?
Gcc compiler is mandatory to have because the exploit is written in C language. Install the gcc compiler if not been installed on the host.
$ sudo apt install gcc
In our case, we have the latest gcc package installed on our machine.
How to Fix the New Ubuntu Overlayfs Vulnerability (CVE-2021-3493) On The Host?
Ubuntu has issued the security advisory to fix this vulnerability. In this security advisory Ubuntu has fixed two vulnerabilities.
https://launchpad.net/ubuntu/+source/linux-oem-5.6
How to fix the new Ubuntu overlayfs vulnerability (CVE-2021-3493) on Ubuntu?
Step 1. Update your Ubuntu OS before you begin
Before we start fixing the issue, update your repositories with this command:
$ sudo apt update
Enter root password to proceed.
Step 2. Install Kernel package
Install the ‘linux-image-5.6.0-1055-oem’ kernel package.
$ sudo apt install linux-image-5.6.0-1055-oem
Enter root password and hit ‘y’ to continue the installation process.
Step 3. Installation of Kernel is in progress…
Step 4. Reboot your Ubuntu Machine
After the completion of the installation. Reboot the system and let the system to boot with new kernel.
$ sudo reboot
Step 5. Check the Kernel version on Ubuntu
Launch terminal after the system reboot. To our surprise we saw a different and latest version of kernel on my system. When we tried exploiting the system as we did earlier. I didn’t get the root command prompt this time. You can see this below.
This is how you can fix the new Ubuntu overlayfs vulnerability (CVE-2021-3493) on the host.
Thanks for supporting our work. Please check in thesecmaster.com for more such tutorials.
Arun KL
Arun KL is a cybersecurity professional with 15+ years of experience in IT infrastructure, cloud security, vulnerability management, Penetration Testing, security operations, and incident response. He is adept at designing and implementing robust security solutions to safeguard systems and data. Arun holds multiple industry certifications including CCNA, CCNA Security, RHCE, CEH, and AWS Security.